Protecting Your Small Business: Essential Cybersecurity Tips
In 2021, approximately 46% of security breaches had an impact on small and medium-sized enterprises (SMBs).
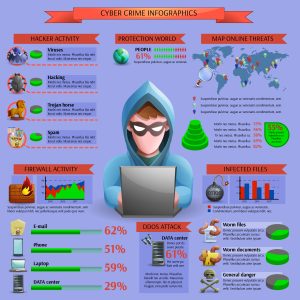
There exists a multitude of cyberattack types, with social engineering attacks such as phishing and denial-of-service attacks being the most common ones affecting SMBs.
To bolster your overall cybersecurity posture, it is advisable to incorporate universally acceptable strategies for staying ahead and protecting your business from cyberattacks.
This article is intended for business proprietors seeking to gain an understanding of cybersecurity and safeguard their companies against cyber threats.
While the exact timing of an attack may remain unpredictable, taking appropriate precautions can thwart or significantly impede a hacker’s efforts to infiltrate your network.
We have compiled useful information explaining why your small business might be susceptible to cyberattacks and how you can protect your business through cybersecurity best practices.

Why Cybercriminals Target Small Businesses:
Verizon’s 2021 Data Breach Investigations Report revealed that 46% of security breaches affected small and midsize businesses.
This may not come as a surprise, as new small business owners often prioritize other aspects of starting a business, inadvertently leaving security vulnerabilities open to exploitation by hackers.
This oversight can have severe consequences.
According to a joint study by IBM and the Ponemon Institute, the average cost of a data breach increased by 10% in 2021. Verizon’s data suggests that the costs associated with 95% of incidents involving SMBs ranged from $826 to $653,587. Furthermore, SMBs often lack the resources needed for effective defense.
Independent researcher and technology risk analyst Stephen Cobb notes that small businesses fall within the sweet spot for cybercriminals, offering more digital assets to target than individual consumers but possessing less security than larger enterprises.
When coupled with the costs associated with implementing robust defenses, this makes them prime targets for intrusion. Security breaches can be devastating for small businesses, often leading owners to pay ransoms to recover their data. SMBs can also serve as stepping stones for attackers seeking access to larger enterprises.
Notable Statistics:
A survey conducted by Digital.com in March 2022 found that 51% of small businesses had not implemented cybersecurity measures.
Types of Cyberattacks to Be Aware Of:
Irrespective of their target, hackers generally aim to gain access to sensitive data, such as credit card information.
Familiarizing yourself with various hacking methods is crucial for preparedness. While this list does not encompass all potential threats, it is essential to be acquainted with the following types of attacks:
Advanced Persistent Threat (APT):
An Advanced Persistent Threat (APT) is a sophisticated and long-term cyberattack strategy typically carried out by highly skilled and organized threat actors, often with the backing of nation-states or well-funded criminal groups.
APTs are characterized by their persistence and stealth, as they aim to infiltrate a target network or system and maintain unauthorized access for an extended period, sometimes months or even years, without being detected.
Key attributes of APTs include:
- Stealthy Approach: APT actors use various techniques, such as social engineering, spear-phishing, and zero-day exploits, to gain initial access to a target. Once inside, they take great care to remain undetected.
- Long-Term Focus: APTs are not opportunistic; they have specific targets and objectives. They patiently gather intelligence, steal data, or disrupt operations over an extended period.
- Adaptability: APT actors often adapt their tactics, techniques, and procedures (TTPs) in response to security measures taken by the target, making them challenging to defend against.
- Use of Advanced Tools: They leverage sophisticated malware, custom-developed exploits, and advanced command and control infrastructure to maintain access and control.
- High Motivation: APT actors are highly motivated, often with political, economic, or strategic goals. They are willing to invest time and resources to achieve their objectives.
- Target Variety: APTs can target a wide range of organizations, including government agencies, corporations, research institutions, and critical infrastructure.
Defending against APTs requires a comprehensive cybersecurity strategy that includes continuous monitoring, threat intelligence sharing, employee training, and the use of advanced security technologies. Organizations must be vigilant and prepared to respond swiftly if an APT breach is suspected to minimize potential damage.
Distributed Denial-of-Service (DDoS) Attack:
A Distributed Denial-of-Service (DDoS) attack is a malicious attempt to disrupt the normal functioning of a network, website, or online service by overwhelming it with a flood of traffic from multiple sources, often controlled by a botnet. The primary goal of a DDoS attack is to make the target system or service unavailable to its intended users.
Key characteristics of DDoS attacks include:
- Distributed Sources: DDoS attacks use a large number of compromised computers, servers, or devices, often spread across the internet, to generate a massive volume of traffic simultaneously.
- High Traffic Volume: The attacker floods the target with a significantly higher volume of traffic than it can handle, consuming its bandwidth, server resources, or network capacity.
- Variety of Attack Types: DDoS attacks come in various forms, such as volumetric attacks (flooding with traffic), application layer attacks (targeting specific software vulnerabilities), and protocol attacks (exploiting weaknesses in network protocols).
- Disruption, Not Data Theft: Unlike other cyberattacks that aim to steal data or gain unauthorized access, DDoS attacks focus on rendering a system or service inaccessible for a temporary period.
- Short-Term Impact: DDoS attacks are generally short-lived but can cause significant downtime and financial losses for the targeted organization.
To mitigate DDoS attacks, organizations employ various defense strategies, including traffic filtering, rate limiting, content delivery networks (CDNs), and specialized DDoS mitigation services. Additionally, monitoring network traffic for unusual patterns and having an incident response plan in place are crucial for minimizing the impact of DDoS attacks.
Inside Attack:
An inside attack in cybersecurity refers to a security breach or malicious activity initiated by someone who already has authorized access to an organization’s internal systems, networks, or data. This person could be an employee, contractor, vendor, or anyone with legitimate credentials or physical access to the organization’s resources.
Inside attacks can take several forms, including:
- Insider Threats: These are individuals within the organization who misuse their privileges intentionally or unintentionally. Motivations can range from financial gain to personal grudges or ideology.
- Compromised Accounts: An attacker may gain access to an employee’s or administrator’s account credentials through methods like phishing, social engineering, or brute force attacks, effectively masquerading as an authorized user.
- Third-Party Vendors: Contractors, suppliers, or service providers with access to an organization’s systems can also pose inside attack risks if they are compromised or act maliciously.
Inside attacks are particularly challenging to prevent and detect because the perpetrators often have a level of trust within the organization.
To mitigate inside threats, organizations implement security measures such as access controls, user monitoring, employee training, and implementing the principle of least privilege, which restricts user access to only what is necessary for their roles.
Regular security audits and incident response plans are also essential to respond effectively when inside attacks occur.
Malware:
A malware attack in cybersecurity involves the use of malicious software, or “malware,” to compromise a computer system, network, or device with the intent of causing harm, stealing data, or gaining unauthorized access. Malware encompasses a wide range of malicious programs, including viruses, worms, Trojans, ransomware, spyware, and more.
Here’s how a typical malware attack unfolds:
- Delivery: Malware is delivered to the target system through various means, such as email attachments, malicious website downloads, infected software, or compromised files.
- Infection: Once on the target system, the malware executes and infects the device or network. Different types of malware have various methods of propagation.
- Execution: The malware carries out its malicious actions, which can include stealing sensitive data, damaging files, encrypting data for ransom, hijacking the system, or creating backdoors for future access.
- Persistence: Malware often attempts to establish persistence by modifying system settings, creating auto-start entries, or concealing itself to evade detection and removal.
- Command and Control (C2): Many types of malware connect to a remote server controlled by the attacker to receive commands, exfiltrate data, or download additional malicious payloads.
- Impact: The ultimate impact of a malware attack can range from mild inconvenience to severe data breaches, financial losses, system downtime, or compromised security.
Cybersecurity measures to defend against malware attacks include using antivirus and anti-malware software, keeping software and systems up to date with security patches, educating users about safe online practices, implementing strong access controls, and regularly backing up data to mitigate the impact of ransomware and data loss.
Man in the Middle (MitM) Attack:
A Man-in-the-Middle (MitM) attack is a cybersecurity threat where an attacker secretly intercepts and potentially alters the communication between two parties, often without their knowledge or consent. This attacker positions themselves between the sender and receiver of data, acting as an unauthorized intermediary.
Key characteristics of a MitM attack include:
- Interception: The attacker intercepts data transmitted between two parties, which can include sensitive information such as login credentials, financial data, or personal communications.
- Unauthorized Access: The attacker gains unauthorized access to the communication channel, typically by exploiting vulnerabilities in the network or by using deceptive techniques like ARP (Address Resolution Protocol) poisoning or DNS (Domain Name System) spoofing.
- Eavesdropping: In a passive MitM attack, the attacker simply listens to the communication, while in an active MitM attack, the attacker may modify or inject malicious content into the data being exchanged.
- SSL/TLS Bypass: Some MitM attacks attempt to bypass the encryption provided by protocols like SSL/TLS, making it appear as though the communication is secure when it is compromised.
MitM attacks can occur in various contexts, including unsecured Wi-Fi networks, compromised routers, or even within an organization’s internal network.
To protect against MitM attacks, users and organizations should use secure and authenticated communication channels, implement strong encryption protocols, regularly update and patch software and devices, and be cautious when connecting to public or untrusted networks.
Password Attack:
A password attack is a cybersecurity attack method in which an attacker attempts to gain unauthorized access to a computer system, user account, or network by guessing, cracking, or stealing passwords. Password attacks exploit weaknesses in password security to compromise the target.
Common types of password attacks include:
- Brute Force Attack: In this attack, the attacker systematically tries every possible combination of characters until the correct password is found. This method can be time-consuming but may eventually succeed if the password is weak.
- Dictionary Attack: This attack involves using a predefined list of commonly used passwords or words from a dictionary to guess the target’s password. It’s more efficient than brute force and is often successful against weak passwords.
- Credential Stuffing: Attackers use previously stolen username and password combinations (often from data breaches) to attempt unauthorized access to various online accounts, exploiting the fact that people often reuse passwords across different services.
- Phishing: In phishing attacks, attackers trick users into revealing their passwords by posing as legitimate entities through fake websites, emails, or messages. Users unknowingly provide their login credentials to the attackers.
- Keylogging: Malicious software, known as keyloggers, is used to record keystrokes on a compromised device, capturing usernames and passwords as users type them.
To defend against password attacks, individuals and organizations should implement strong password policies, encouraging the use of complex and unique passwords, multi-factor authentication (MFA), and regularly updating passwords. Additionally, monitoring for unusual login attempts and promptly addressing any breaches or suspicious activities is crucial for security.
Phishing:
Phishing is a cyberattack technique in which attackers impersonate trusted entities, such as legitimate organizations or individuals, to deceive victims into taking specific actions, typically divulging sensitive information like usernames, passwords, credit card details, or clicking on malicious links. Phishing attacks are often carried out through emails, but they can also occur via text messages, social media, or other communication channels. In the unfortunate event of such an incident, your company stands to face significant consequences. Customer and partner trust may erode, potentially leading them to seek services elsewhere, ultimately resulting in financial losses for your business
Key characteristics of phishing include:
- Deception: Phishers craft messages or websites that appear legitimate to trick victims into believing they are interacting with a trustworthy source.
- Manipulation: Phishing messages often use urgency, fear, or curiosity to manipulate recipients into taking immediate action, like clicking on a link or providing personal information.
- Spoofing: Attackers can easily impersonate legitimate organizations by spoofing email addresses or creating fake websites that mimic the appearance of the real ones.
- Diverse Targets: Phishing attacks can target individuals, organizations, or specific departments within organizations, depending on the attacker’s goals.
- Payloads: Phishing attacks may lead to various consequences, such as stealing login credentials, distributing malware, or spreading ransomware.
To defend against phishing, individuals and organizations should be cautious when receiving unsolicited messages, verify the authenticity of requests for sensitive information, check email sender addresses carefully, avoid clicking on suspicious links, and use email filtering and cybersecurity tools designed to detect and block phishing attempts.
Security awareness training is also crucial in educating individuals about recognizing and responding to phishing threats.
Tech Support Scams:
Receiving Suspicious Phone Calls, Pop-Up Messages, or Emails About Computer Issues
Frequently, these calls, pop-up notifications, and emails are orchestrated by scammers with the intention of obtaining your money, personal data, or access to your files. Such actions can jeopardize your network, expose your data to risks, and harm your business.
How the Scam Operates:
The scammers often pose as representatives of well-known tech companies, like Microsoft. They employ technical jargon to persuade you that your computer is genuinely experiencing issues. They might request that you open certain files or run computer scans, asserting that these actions reveal problems, even when there are none.
- Subsequently, the scammers might request remote access to your computer, enabling them to view all stored information, including data on connected networks. They may also attempt to:
- Enroll you in dubious computer maintenance or warranty programs.
- Install malware that grants them access to your computer and sensitive data, such as usernames and passwords. Solicit your credit card information to bill you for fictitious services, or services readily available elsewhere for free.
- Attempt to sell you software or repair services that hold no value or are accessible elsewhere at no cost.
- Direct you to websites, urging you to input credit card, bank account, and other personal information.

Vendor Security:
Ensuring the Protection of Sensitive Information Shared with Business Vendors. It’s crucial to verify that our business vendors are taking adequate measures to secure their computer systems and networks.
For instance, consider the scenario where your accountant, who has access to your financial data, loses their laptop. Or if a vendor with interconnected networks experiences a security breach.
The potential consequence is the exposure of your business data and your customers’ personal information to unauthorized parties, thereby jeopardizing your business and customer security.
Monitoring Vendor Security:
- Document Security Measures: Embed security provisions in your vendor contracts, outlining plans for evaluating and enhancing security controls to adapt to evolving threats. These security provisions should be non-negotiable and tailored to your company’s critical needs.
- Validate Compliance: Establish procedures to independently confirm that vendors adhere to your security requirements. Relying solely on their assurances may not be sufficient.
- Adapt to Changing Threats: Given the rapidly evolving landscape of cybersecurity threats, ensure that your vendors continuously update their security measures.
Protecting Your Business:
- Implement Access Controls: Enforce stringent controls on databases housing sensitive information. Limit access strictly to individuals with a need-to-know basis and for the duration necessary to complete specific tasks.
- Data Safeguarding: Utilize properly configured, robust encryption methods to safeguard sensitive data during transmission and storage.
- Network Security: Enforce the use of strong passwords, consisting of a minimum of 12 characters that include a combination of numbers, symbols, uppercase, and lowercase letters. Avoid password reuse, sharing, and implement limits on unsuccessful login attempts to thwart password-guessing attacks.
- Employ Multi-Factor Authentication: Require vendors to employ multi-factor authentication, necessitating additional verification steps beyond password entry, such as temporary codes sent to smartphones or the use of physical keys.
- By diligently following these measures, you can enhance the security of sensitive information shared with your business vendors and mitigate potential risks to your business and customers.

Selecting a Web Hosting Service:
Considering a New or Enhanced Website for Your Business: If you’re looking to create a new website for your business or upgrade an existing one, but lack the expertise to set it up yourself, hiring a web hosting provider may be a smart choice.
There is an abundance of web hosting options available, whether you’re revamping your current site or launching a new business. However, when evaluating these services, security should be a paramount concern.
Key Factors to Examine:
Transport Layer Security (TLS): Ensure that the service you opt for includes TLS, as it plays a crucial role in safeguarding your customers’ privacy. TLS, the successor to Secure Sockets Layer (SSL), helps confirm that users land on your legitimate website when entering your URL in the address bar. When TLS is properly implemented on your website, your URL will commence with “https://.”
TLS also ensures that data sent to your website is encrypted, which is especially vital if you collect sensitive information such as credit card details or passwords.
Email Authentication: Some web hosting providers enable you to establish business email accounts using your domain name, an integral part of your URL and what represents your website’s identity (e.g., yourbusiness.com). Your business email will typically appear as something like name@yourbusiness.com. Lacking proper email authentication measures, malicious actors can impersonate your domain and send fraudulent emails appearing to be from your business.
Verify that your web host can offer these three email authentication tools:
- Sender Policy Framework (SPF)
- Domain Keys Identified Mail (DKIM)
- Domain-based Message Authentication, Reporting & Conformance (DMARC)
Software Updates: Many web hosting providers provide pre-built websites or software packages designed for quick and easy website setup. Similar to any software, it’s imperative to use the latest versions that incorporate up-to-date security patches. Determine whether you are responsible for keeping the website’s software current or if the web host provider will manage this for you.
Website Management: Clarify the arrangement for website management with your web host provider. In some cases, the provider may handle all changes, while in others, you might have the option to make certain adjustments yourself. It’s essential to establish who will manage the website once it’s built from the outset.
Key Questions to Ask:
When engaging a web host provider, these inquiries can help ensure the protection of customer information and your business data:
- TLS Inclusion: Is TLS part of the hosting plan, and is it offered as a complimentary inclusion or as a paid add-on? Will I be responsible for setting it up, or will you assist me in configuring it?
- Software Updates: Are the most recent software versions available with your service, and will you ensure their ongoing updates? If it’s my responsibility to maintain software updates, is the process user-friendly?
- Email Authentication: Can my business email be associated with my business website name, and can you aid in implementing SPF, DKIM, and DMARC email authentication technologies? If not, should I consider a provider that offers these services?
- Website Management: After the website’s setup, who will have the authority to make modifications? Will changes require your intervention, or will I have the autonomy to log in and make adjustments independently? If self-management is possible, is multi-factor authentication available for added security?

Ransomware:
Ransomware is a type of malicious software (malware) that encrypts a victim’s files or locks them out of their computer system, rendering their data inaccessible. The attacker then demands a ransom payment, typically in cryptocurrency, in exchange for a decryption key or to regain access to the affected system.
Key characteristics of ransomware include:
- Encryption: Ransomware uses strong encryption algorithms to lock the victim’s files or system, making it nearly impossible to recover data without the decryption key.
- Ransom Demand: After encrypting the files or system, the attacker displays a ransom note on the victim’s screen, demanding payment to provide the decryption key. The ransom note often includes instructions for making the payment.
- Payment in Cryptocurrency: Ransom payments are usually demanded in cryptocurrencies like Bitcoin to help the attacker remain anonymous.
- Data Extortion: Some ransomware strains have evolved to include data theft, where attackers threaten to publish or sell stolen data if the ransom is not paid.
- Wide Range of Targets: Ransomware can target individuals, businesses, government agencies, and organizations of all sizes.
Ransomware attacks can have severe consequences, including data loss, financial losses, and operational disruptions. To protect against ransomware, individuals and organizations should regularly back up their data, keep software and systems up to date, use strong and unique passwords, employ security software, and educate users about safe computing practices. Additionally, a robust incident response plan is essential to minimize damage in case of an attack.

SQL Injection Attack:
An SQL Injection (SQLi) attack is a type of cyberattack that targets databases through vulnerabilities in web applications. In an SQL Injection attack, an attacker inserts malicious SQL (Structured Query Language) code into input fields or data forms on a website. When the web application processes this input without proper validation or sanitization, the injected SQL code can manipulate the database and potentially grant the attacker unauthorized access to data, modify, or delete data, or even execute administrative operations on the database server.
Key characteristics of SQL Injection attacks include:
- Injection Point: Attackers identify vulnerable input fields, such as search boxes or login forms, to inject malicious SQL code.
- Malicious SQL Code: The attacker injects SQL code that can exploit vulnerabilities like missing input validation, lack of parameterized queries, or poor coding practices.
- Unauthorized Access: SQL Injection attacks can result in unauthorized access to sensitive data, data manipulation, or even control over the database server.
- Data Theft: Attackers may steal data, such as usernames, passwords, or confidential information, from the database.
- Data Modification or Deletion: In some cases, attackers can modify or delete data within the database, causing data loss or damage.
To prevent SQL Injection attacks, developers should implement secure coding practices, use parameterized queries or prepared statements, sanitize user inputs, and conduct security testing to identify and fix vulnerabilities. Web application firewalls (WAFs) and security monitoring can also help detect and prevent SQL Injection attempts.

Zero-Day Attack:
A zero-day attack is a type of cyberattack that exploits a software vulnerability or security flaw in a computer program, operating system, or application that is not yet known to the software developer or the public. These vulnerabilities are called “zero-day” because there are zero days of protection against them since no official patch or fix exists at the time of the attack.
Key characteristics of zero-day attacks include:
- Hidden Vulnerability: Attackers discover and exploit the vulnerability before the software developer becomes aware of it, leaving users and organizations vulnerable.
- No Patch Available: Since the vulnerability is unknown, there is no official patch or update to protect against the attack.
- Stealthy Exploitation: Zero-day attacks are often used for targeted and stealthy cyberespionage or cybercriminal activities, as they offer a significant advantage to attackers.
- High Value Targets: High-profile organizations, government agencies, or individuals with valuable data are often targeted in zero-day attacks.
To defend against zero-day attacks, organizations should employ best practices for cybersecurity, such as regularly updating software and systems, implementing intrusion detection systems, using security monitoring, and staying informed about emerging threats through threat intelligence sources. Additionally, security researchers and organizations should responsibly disclose newly discovered vulnerabilities to software vendors so that patches can be developed and distributed to protect users.

Securing Your Networks:
As more businesses expand online, robust cybersecurity measures become increasingly essential.
According to Cybersecurity Ventures’ 2022 Cybersecurity Almanac, global spending on cybersecurity products is projected to reach $1.75 trillion between 2021 and 2025, up from $1 trillion between 2017 and 2021.
To provide at least a basic defense against various cyber threats, small businesses should consider:
- Antivirus solutions for protection against most types of malware.
- Firewalls, which can be hardware- or software-based, to prevent unauthorized access.
- Data backup solutions for quick data recovery in case of a breach.
- Encryption software to safeguard sensitive data.
- Two-step authentication or password-security software for enhanced password protection.
- Conducting a risk assessment, either independently or with external assistance, is advisable when considering cybersecurity measures.
- Cybersecurity Best Practices: In addition to implementing software-based solutions, adopting technological best practices and policies is crucial for enhancing security. Key practices include:
- Keeping software up to date to mitigate vulnerabilities.
- Educating employees about cybersecurity threats and best practices.
- Implementing and enforcing security policies throughout the organization.
Developing and practicing an incident response plan to minimize damage during a cyberattack.
While cybercrime continues to evolve, cybersecurity solutions are becoming more sophisticated as well. There are numerous methods to secure devices and networks, along with secure file sharing options. It is important not to become complacent, but by adhering to best practices, your business can maintain digital security and resilience.

